UF Cybersecurity Framework (CSF)
 In July 2021, the University of Florida established the UF Cybersecurity Framework (UFCSF) Program to begin assessing the cybersecurity maturity of business processes using a customized framework based on the NIST Cybersecurity Framework (CSF) to help business units understand and manage cybersecurity risks. The UFCSF Program is maintained to the current version of the NIST CSF to ensure continued alignment with current cybersecurity standards and best practices.
In July 2021, the University of Florida established the UF Cybersecurity Framework (UFCSF) Program to begin assessing the cybersecurity maturity of business processes using a customized framework based on the NIST Cybersecurity Framework (CSF) to help business units understand and manage cybersecurity risks. The UFCSF Program is maintained to the current version of the NIST CSF to ensure continued alignment with current cybersecurity standards and best practices.
Enhanced view of cybersecurity risks

UF already conducts cybersecurity risk assessments at the information system level, providing a detailed understanding of the risks associated with individual systems. While this provides valuable insight, it focuses primarily on specific technologies rather than the broader operational cybersecurity posture across the university.
The UFCSF expands this by providing a high-level view of cybersecurity maturity across participating units. These results will be combined to create a university-wide maturity rating, helping leadership better understand overall cybersecurity risk and opportunities for improvement.
The UFCSF assessment provides insight that helps the university:
- Develop a clearer, unified view of the university’s overall cybersecurity posture
- Identify gaps in cybersecurity processes, technology, and practices across the institution
- Support the Enterprise Risk Register by highlighting institutional cybersecurity risks
- Identify and develop university-wide solutions that can most effectively reduce risk and strengthen cybersecurity maturity
- Provide guidance to units on areas where cybersecurity practices can be improved and documented in their Information Security Plan
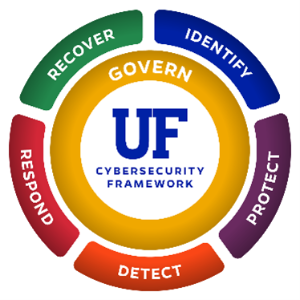
Organized around the 6 functions of the NIST Cybersecurity Framework
The NIST Cybersecurity Framework organizes cybersecurity practices into six core areas that represent how organizations manage cybersecurity risk. These functions define the scope for assessment and help provide a structured way to evaluate cybersecurity activities across the university and identify opportunities for improvement.
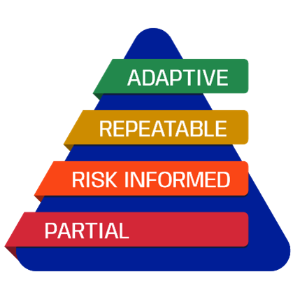
The NIST CSF assesses against the functions using implementation tiers that describe the level of cybersecurity maturity with the business processes. These tiers range from Partial (Tier 1) to Adaptive (Tier 4) and provide context for how consistently and effectively cybersecurity practices are implemented across the university.
Each function represents a key part of managing and strengthening cybersecurity across the organization.
- Govern: Ensuring cybersecurity is properly managed, supported by leadership, and aligned with university policies and risk management.
- Identify: Understanding what systems, data, and services exist and the risks that may affect them.
- Protect: Implementing safeguards to help secure systems, information, and university resources.
- Detect: Monitoring systems and activities to identify potential security events as quickly as possible.
- Respond: Taking action to contain and manage cybersecurity incidents.
- Recover: Restoring systems and services after an incident and improving resilience moving forward.
Assessment Process
Assessment of business units against the UFCSF is conducted through a survey initiated from the UF Information Risk Management (IRM) system. Unit OneIT Leaders define the organizational units in scope for assessment and identify the appropriate technical contact for completing the survey. Assessment of units against the UFCSF occurs biennially to provide time for units to address gaps and update their information security plan prior to the next assessment cycle.

The assessment survey is organized around the NIST CSF categories and subcategories that are in scope for unit assessment. Following assessment completion, the results are made available to the Office of Internal Audit for review and validation as part of a continuous monitoring process to assist with maintaining consistency across cybersecurity practices. Assessment results are further refined to produce overall maturity metrics for units and the university from the aggregated data. Gaps identified in cybersecurity practices are made available to leadership review to guide in remediation efforts.
UFCSF Q & A *Coming soon
